The most outstanding accomplishment of human scientific endeavor to date occurred on July 20, 1969, when two mortals stepped on the lunar surface. This monumental feat was accomplished due to advances in rocketry and colossal (at that time) improvement in computing power.
Russia-Ukraine War ‘Expands’ As Russia-NATO War; Moscow Threatens On Attacking Crimea Or Using F-16 Fighters
Incidentally, the computing power that enabled man on the moon was merely equivalent to a Pentium one of the present times.
Computing power increases exponentially and is governed by Moore’s law: “Computing power doubles yearly.” Today’s Xbox is nearly 1000 times faster than a Pentium One, maybe more.
A physicist in the USA, who needed supercomputer assistance for his research but failed to buy the computer time due to prohibitive cost, found a peculiar yet workable alternative. He purchased more than 1000 Xboxes, put them in parallel, and achieved the computing power required for research.
Growth in computing power has improved information sharing and created a new domain of warfare – information warfare (IW). IW experts have developed the ability to ‘hack’ into a supposedly impregnable computer network protected by numerous firewalls.
Hacking As A Profession
‘Hacking’ has emerged as the most potent soft weapon in IW. It destroys, corrupts, de-regulates, and alters the original program and can introduce undesirable inputs in the software controlling the network that may lead to catastrophe.
For example, it has been alleged that Russian hackers intervened in the power grid in Ukraine in 2015, causing widespread darkness for a considerable period.
IW has been defined as “Conflict and/or struggle between two or more groups in the information environment.” To interfere with computer networks controlling the nuclear reactors, power grid, and airline/railway ticketing system, to name a few, and virtually all other domains of almost all nations, experienced software specialists are required to attempt illegal and illegitimate transgressions into the networks.
According to a World Bank study, Russia has ‘invested’ heavily in this sphere and has over one million software specialists.
It is believed that ‘officially monitored/controlled’ groups of cyber warriors numbering around three dozen are actively involved in hacking/attempting to hack other nations’ networks. Needless to emphasize, this form of warfare is more potent and can reap incredible benefits without being identified.
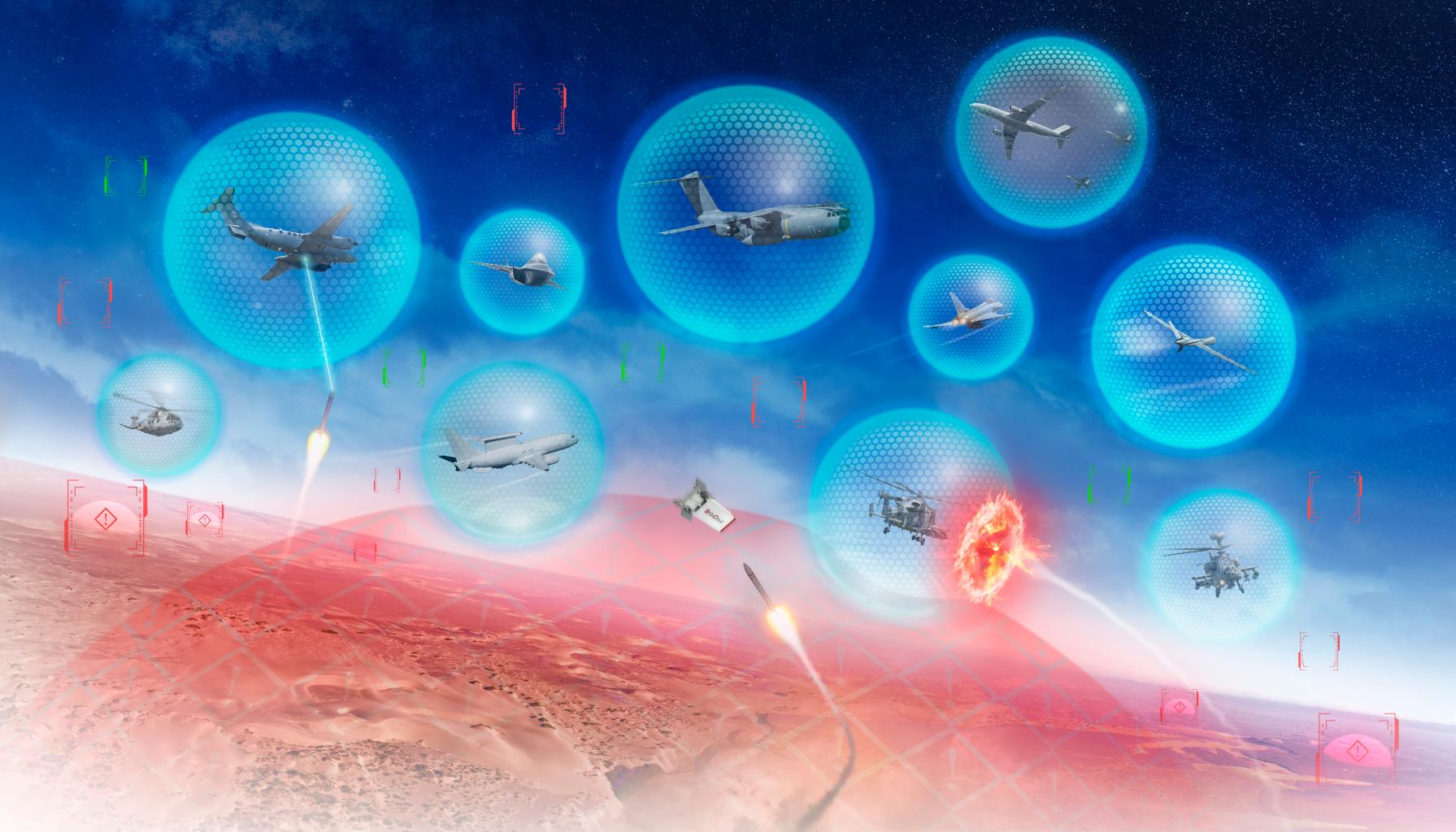
Shifting focus from system hacking to platform hacking opens up far greater possibilities. UAVs and UCAVs are the future of aerial warfare. Imagine a scenario wherein the adversary’s UAV/UCAV is taken over by an unidentified entity and used against the originator.
Such eventualities are no longer fictional and could be a reality in the next ‘big’ conflict.
Cyberattacks
Currently, cyberattacks are confined to gathering intelligence by stealing/accessing sensitive information, defacing the home page, leaving warning messages, and in a few cases, espionage.
Iranian hackers have previously tried to identify computers that control infrastructure in the US, targeted a small dam in New York’s Westchester County, and launched distributed denial-of-service (DDoS) attacks on US banks designed to slow service to a crawl.
US authorities established that hacking operations took place during Iranian working hours and corresponded to the country’s work week of Saturday to Wednesday.
Department of Defense warned US contractors about Shamoon, an Iran-linked malicious program that wiped out thousands of computers in Saudi Arabia. Investigating team opined, “We assess there may be multiple Iran-based threat groups capable of carrying out destructive operations.”
A common belief is that website of the National Security Agency (NSA) of the USA is one of the most impregnable networks. But the hackers of unknown nationalities (possibly Russians) hacked into the website and stole highly classified material.
It stunned the US lawmakers and the intrusion in 2015 was not made public knowledge for nearly two years. Wall Street Journal called it “one of the most significant security breaches in recent years.”
Detailed investigation revealed that the hack was possible because Kaspersky Lab’s anti-virus software identified the files. This a classic case of the ‘Guard involved in the theft.’
It might be termed a travesty of fate when viewed in the context that the US interfered with the Iranian centrifuge network by introducing the STUXNET virus through one of the Iranian engineers working in the facility and was using the device on his home computer as well.
An identical act was performed when an NSA contractor took the files home without authorization, and they were accessed by attackers on that person’s home computer, which was running Kaspersky Lab’s software.
The stolen material included details about how the NSA penetrates foreign computer networks, the code it uses for such spying, and how it defends networks inside the US.
The US has identified Russia as the primary culprit actively involved in hacking activity against the West, US in particular. Russians are resorting to digital intrusions, which have crippled networks, and they continue to refine their expertise with knowledge gained from each such intrusion.
Russian & North Korean Hackers
Russian hackers’ interference in US presidential elections in 2016 is a well-known fact. Hackers working for the Russian government successfully penetrated the voter rolls of a few states, according to Jeannette Manfra, the head of cyber security in the Department of Homeland Security.
Manfra told NBC News that the hackers targeted 21 states, and an “exceptionally small number” of states were successfully accessed.

North Korea’s cyber army appears to be going after real weapons. Hackers tied to Kim Jong Un’s regime stole blueprints and other information about warships and submarines last year when they broke into one of the world’s biggest shipbuilders, according to South Korean lawmaker Kyeong Dae-soo.
North Korean hackers association with Pakistan might spell trouble for India.
Indian Initiative, Capability & Vulnerability
Are we in India looking at the issue of ‘hacktivism’ with the seriousness it deserves? Merely placing numerous firewalls is not adequate security. We must discipline ourselves to eliminate our culture of doing official work on our personal computers linked to the internet.
Although we call ourselves a ‘software superpower,’ the fact is that we do not produce a single computer chip. Everything is imported. Embedded viruses, viz Trojan Horse, etc., are known to be activated by the manufacturing country at the time of their choosing.
China has progressed by leaps and bounds in acquiring advanced chip technology. China is in the process of developing the fastest supercomputer.
Indian efforts towards becoming a nation of ‘competent hackers’ are far away. We are particularly vulnerable to hacking due to our flawed propensity towards “everyone keeping every record” in soft and/or hard copy.
Our ‘computer discipline’ at all levels is no better than a hooligan on the street using a smartphone. For example, during Op Parakaram, a software engineer purchased a few hard discs from a flea market in Gwalior.
From one of the hard discs, he extracted the entire war plan of the Mirage-2000 squadron. The logistics section of the station disposed of the concerned hardware to a scrap dealer.
From what is known in the public domain, nothing substantial is being done to enhance IW capability, and ‘HACK’ is just another four-letter word.
- Gp Cpt TP Srivastava (Retd) is an ex-NDA who flew MiG-21 and 29. He is a qualified flying instructor. He commanded the MiG-21 squadron. He is a directing staff at DSSC Wellington and chief instructor at the College of Air Warfare. VIEWS PERSONAL OF THE AUTHOR
- The Author Tweets at @capt_tp
- Follow EurAsian Times on Google News




